APPENDIX: TECHNICAL DEEP DIVE AND RESOURCES
Activating SOS and Medical ID on Smartphones
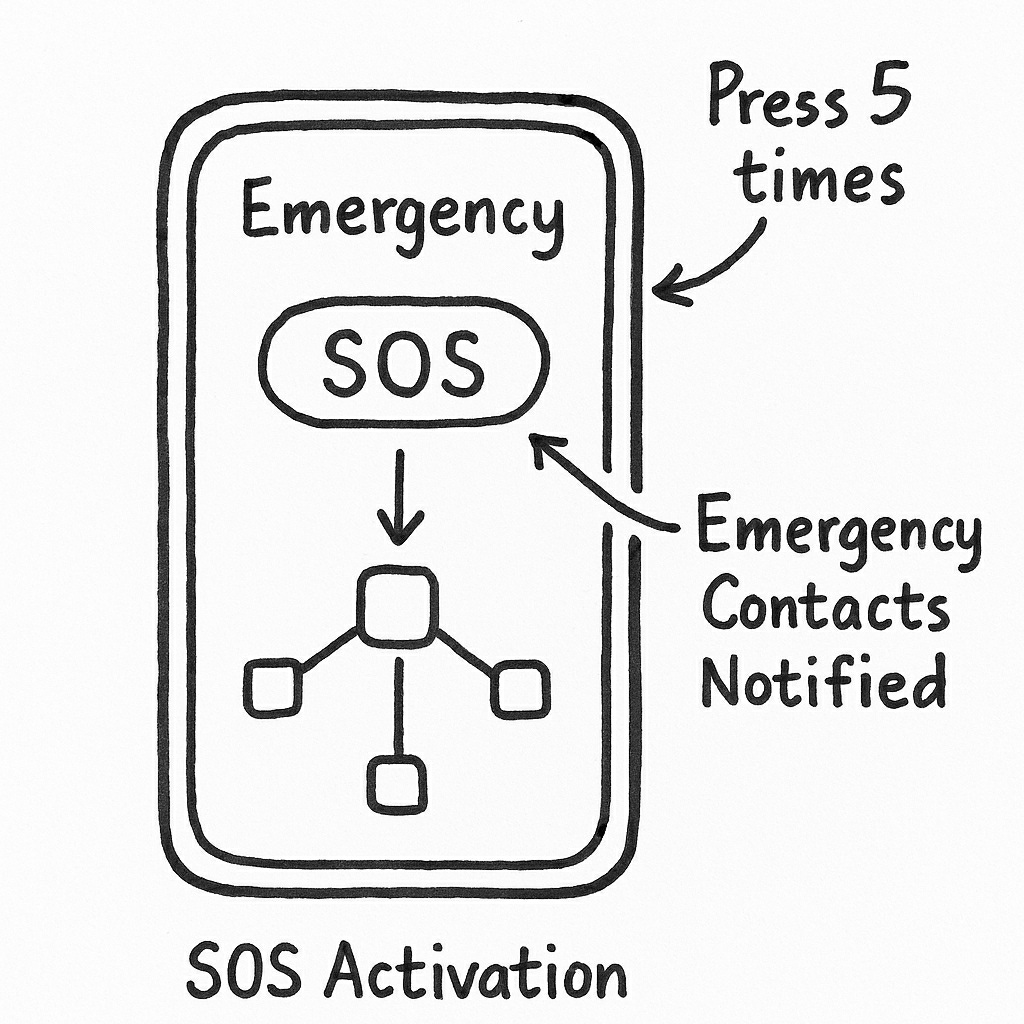
Most smartphones today have an SOS mode built in. With just a few taps—or by pressing the power button several times—you can instantly dial local emergency services. Many devices also send a text to your chosen contacts, sharing your live location and updating it as you move. In a real crisis, muscle memory matters more than you’d expect.
Finding SOS On Your Phone
On an Apple iPhone: Open Settings > Emergency SOS. Enable “Call with Hold and Release” (side button + volume) or “Call with 5 Presses”.
On an Android phone: Open Settings > Safety & Emergency (or search for Emergency SOS). Turn on the feature and choose your activation method.
Setting Up Medical ID
A Medical ID profile stores essential health info (allergies, conditions) accessible from the lock screen.
- iPhone: Health app > Profile Picture > Medical ID > Edit. Ensure "Show When Locked" is ON.
- Android: Settings > Emergency Information. Add blood type and contacts; access via the Emergency button on the lock screen.
Technical Deep Dive on Mesh Networking
This section explores the mechanics behind the distributed architectures mentioned in the book.
1. Network Models
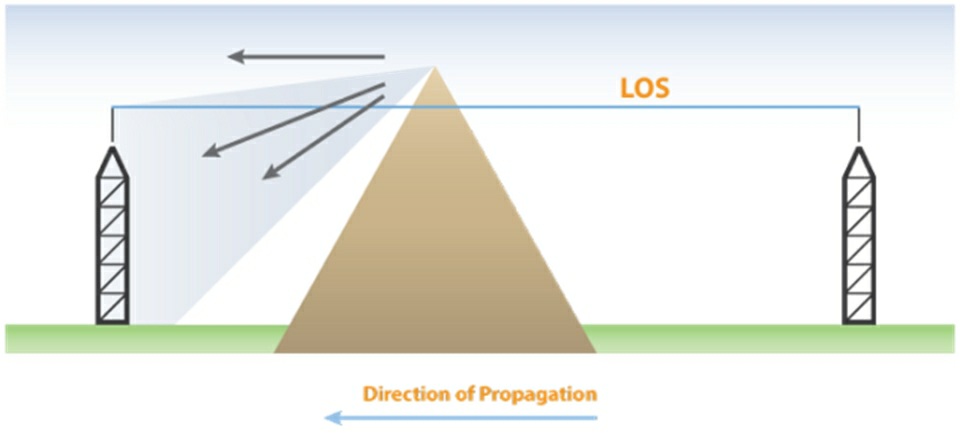
- Centralized (Hub-And-Spoke): Wi-Fi routers and cell towers. If the hub fails, the network collapses.
- Traditional Mesh: Requires nodes to maintain a full map of the network, which becomes inefficient as it grows.
- Modern Mesh (B.A.T.M.A.N.-Style): Nodes only know direct neighbors; routing is adaptive and self-healing, mirroring ant colonies or weather patterns.
2. Encryption: Protecting the Relay
Because mesh messages relay through others' nodes, AES-256 (Advanced Encryption Standard) is the backbone of security. It provides end-to-end protection, ensuring intermediate nodes cannot view or alter contents.
ISM Frequencies by Country
| Region | Frequency Band | Regulation Note |
|---|---|---|
| United States | 915 MHz | No license required; encryption allowed. |
| Europe | 868 MHz | Strict duty cycle limits. |
| Australia | 915–928 MHz | LoRa compatible. |
| China | 470–510 MHz | Regional variance. |
3. Hardware and Power Systems
A typical LoRa Node (like LilyGO or RAK Wireless) consists of an ESP32 MCU, an SX1262 radio, and an optional GPS module. These can be powered by 18650 Li-ion cells, 5–20W solar panels with charge controllers, or vehicle USB ports.
4. Routing and Compliance
- B.A.T.M.A.N.: Highly adaptive and self-healing.
- GMRS (USA): Licensed service (462/467 MHz); no exam required; encryption prohibited.
- HAM Radio: Requires Technician/General/Extra license; encryption prohibited.
- Meshtastic: Uses ISM bands; encryption is allowed.
Resources and Further Reading
- Meshtastic Official: meshtastic.org
- CHIRP Software: chirpmyradio.com
- EFF Privacy Guides: eff.org
- B.A.T.M.A.N. Protocol: Wikipedia Reference
About the Author
Morgan Cade is a writer specializing in technology and real-world problem-solving. An advocate for practical strategies over panic, Morgan's work focuses on community resilience and digital safety.